IMPORTANT SECURITY NOTICE
RTF (Rich Text Format) documents can now been crafted in such a way that they can open a security vulnerability on your computer via Microsoft Office 2003, 2007, 2010, 2013 in Windows and Office 2011 for Mac.
We have received notification from the University OxCERT Security Team (part of IT services) that they have received reports of malicious RTF email attachments being received by University users.
Please exercise extreme caution when opening or previewing email attachments. The RTF exploit can even be triggered by just previewing an RTF attachment from within Microsoft Outlook.
At the moment there is only a partial “fix” for Windows users which disassociates / uncouples the automatic opening of RTF documents from Microsoft Word. It does *not* fix the vulnerability.
Windows user – Follow the link below to the Microsoft “Fix it” website
https://support.microsoft.com/kb/2953095
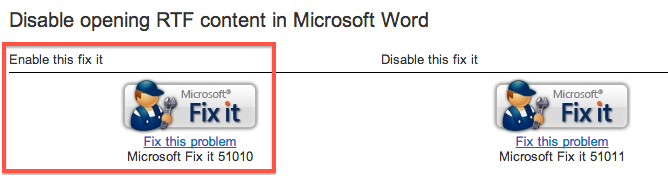
You will see two “Fix it” buttons – see image below – click the left-hand button to “Enable this fix it” (the right-hand button will Disable the “fix”). Then follow the instructions to ‘Run‘ the download.
Go to “Fix it” page here – https://support.microsoft.com/kb/2953095
Mac OS X users – mitigating risk of RTF vulnerability in Microsoft Office 2011 for Mac
All we can suggest at the moment is that you change your default Application for RTF files to something other than Microsoft Word – for instance TextEdit.
- Open TextEdit on your Mac
- Create a new RTF (Rich Text Format) document and save it to your Desktop
- Close TextEdit
- Right-click the RTF document you just created and a context menu will appear showing “Open with >” as an option
- Now with the context menu still open press the Alt key (located to the left of the spacebar) and the “Open with >” menu item will change to “Always Open with >“
- Select “Always Open with > TextEdit“
- All RTF documents will now open TextEdit
- NB : you should remember that this does not patch the vulnerability and your computer can still be compromised should you open a poisoned RTF file with Word 2011 for Mac.
